
HIPAA-Compliant Data Integration Tools for Healthcare: A Complete Guide
Healthcare Technology
Updated Mar 16, 2026
The integration layer is the primary HIPAA risk—secure PHI with AES‑256, TLS 1.3, signed BAAs, strict audit logging, and pass‑through architectures.
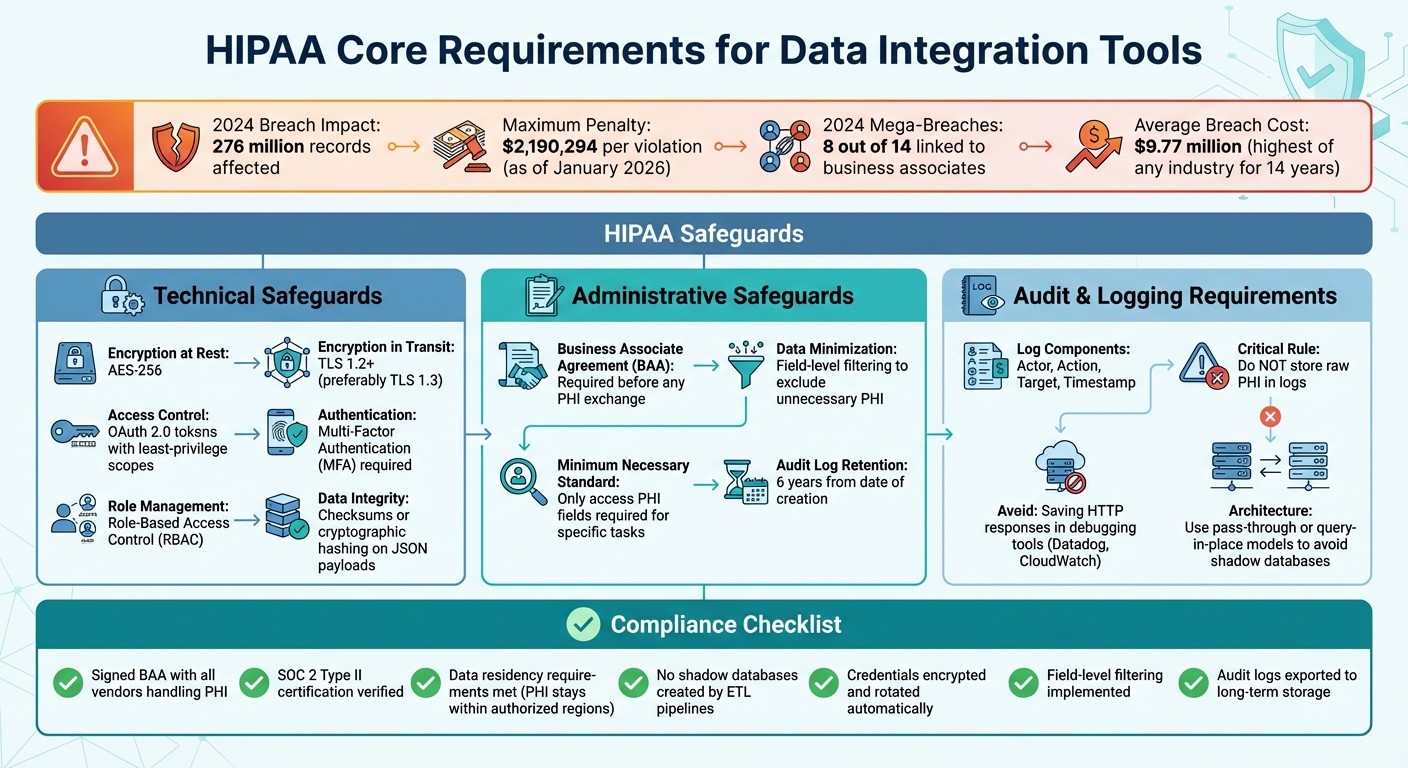
Healthcare data breaches are costly and common. In 2024, breaches affected over 276 million records, with penalties for non-compliance reaching $2.19 million per violation. This guide breaks down what you need to know about HIPAA-compliant data integration tools to protect sensitive patient data while improving system workflows.
Key Takeaways:
Security Requirements: Tools must use AES-256 encryption, TLS 1.2+ (preferably TLS 1.3), OAuth 2.0, and Multi-Factor Authentication (MFA).
Audit Controls: Logs should capture actor, action, target, and timestamp, but avoid storing raw Protected Health Information (PHI).
Business Associate Agreement (BAA): Required for any vendor handling PHI.
Challenges: Legacy systems, shadow databases, and outdated protocols like HL7 v2 can increase risks.
Best Practices: Use pass-through architectures, field-level filtering, and ensure data stays within authorized regions.
The right integration tools simplify compliance while safeguarding patient data. Solutions like Lead Receipt combine security with automation, offering flat-rate pricing and built-in compliance features for healthcare practices.
HIPAA CRM Integration Solutions - Everything you need to know and more
What HIPAA Compliance Means for Healthcare Data Integration
HIPAA-Compliant Data Integration: Core Requirements and Implementation Checklist
HIPAA compliance in data integration creates a framework to protect patient data during every exchange. For example, when connecting an Electronic Health Record (EHR) system to a Customer Relationship Management (CRM) platform or a billing system, you're enabling Protected Health Information (PHI) to move between systems. Each connection must meet strict security standards to avoid exposing patient records - and the penalties for non-compliance can be steep, reaching up to $2,190,294 per violation as of January 2026 [2].
The integration layer, often referred to as the "hot zone", is where credentials, API keys, and PHI are most vulnerable. As Truto explains:
"The single biggest compliance risk you face isn't your core application - it's your integration layer." – Truto [2]
This vulnerability is evident in the numbers. In 2024, 8 out of 14 mega-breaches were linked to business associates - third-party vendors managing integration, hosting, or middleware services [2]. A notable example is the February 2024 ransomware attack on Change Healthcare. This incident disrupted pharmacy payments nationwide and cost billions, all due to compromised credentials and the absence of Multi-Factor Authentication (MFA) on a critical server [2].
Core HIPAA Requirements for Data Integration
Any integration tool handling PHI must adhere to three safeguard categories: technical, administrative, and physical. From a technical standpoint, data must be encrypted during transit using TLS 1.2+ (ideally TLS 1.3) and at rest with AES-256 encryption [1][2]. Access control measures like OAuth 2.0 tokens, MFA, and Role-Based Access Control (RBAC) are essential [1][7].
Audit logging is another critical component. Logs should record details like actor, action, target, and timestamp - without storing raw PHI [2][7]. A common mistake is saving HTTP responses in debugging tools such as Datadog or CloudWatch, which can instantly violate HIPAA [2]. Additionally, logs must be retained for six years from the date of creation [6].
Business Associate Agreements (BAAs) are a cornerstone of HIPAA compliance. Any vendor that creates, receives, maintains, or transmits PHI - including cloud providers and middleware platforms - must sign a BAA before any data exchange occurs [2][8]. Without this agreement, sharing PHI constitutes a direct violation.
The "minimum necessary" standard also plays a key role. Integration tools should only access the PHI fields required for a specific task. For instance, a billing system that only needs patient names and procedure codes should not receive full medical histories or Social Security numbers [2][4].
Despite these safeguards, real-world integration comes with its own set of hurdles.
Common Challenges in Healthcare Data Integration
Even with robust security measures in place, outdated systems and protocols present major obstacles. Many legacy platforms lack modern APIs, forcing organizations to rely on less secure methods like batch transfers, manual exports, or even faxing - which, despite its prevalence, has a 12% failure rate [4]. When APIs are available, they often use outdated protocols like HL7 v2, requiring complex mapping to more modern FHIR standards. This process can introduce errors and compromise data integrity [1].
Traditional ETL (Extract, Transform, Load) pipelines add another layer of complexity. These pipelines often create "shadow databases" by copying PHI from the source EHR into staging tables and then into a data warehouse. Each copy increases the attack surface, requiring its own encryption, monitoring, and audit controls [2][3]. To address this, modern architectures are shifting toward query-in-place or pass-through proxy models, which process data directly in memory without writing PHI to disk [2][3].
Credential security is another critical issue. The integration layer often stores OAuth tokens and API keys, and if these credentials are compromised, attackers can gain prolonged access to patient records. To mitigate this risk, tokens must be encrypted with the same rigor as PHI and rotated automatically using managed vaults [1][2].
Another common oversight is misunderstanding the "conduit exception" in HIPAA. This narrow exemption applies only to basic transmission services, such as postal mail, and does not extend to SaaS platforms or API gateways [2]. Many organizations mistakenly assume otherwise, exposing themselves to compliance risks.
These challenges illustrate the disconnect between regulatory requirements and the practical realities of healthcare data integration.
Key Features to Look for in HIPAA-Compliant Data Integration Tools
When selecting integration platforms for healthcare, it’s essential to focus on features that ensure compliance and minimize the risk of breaches. The right tool should handle encryption, access control, and audit logging automatically, without requiring manual setup for each workflow. It also needs to integrate smoothly with your existing EHR and CRM systems while supporting healthcare data standards like HL7 and FHIR.
Security and Privacy Controls
To meet HIPAA’s strict security requirements, the platform should enforce TLS 1.2 or higher (with plans to adopt TLS 1.3 by 2026) and use AES-256 encryption. Role-Based Access Control (RBAC) is also critical to limit access to sensitive data.
Every interaction involving PHI must be logged in an immutable audit trail that captures essential metadata, such as the actor, action, target, and timestamp [1]. However, to avoid exposing PHI within logs, only metadata should be recorded (e.g., actor, action, timestamp) [2].
Additional safeguards include field-level filtering and row-level security to minimize unnecessary exposure to PHI. Platforms should also adopt pass-through architectures that prevent the creation of shadow databases [2].
These measures not only protect sensitive information but also lay the groundwork for seamless system integration.
System Integration Options
Pre-built connectors for EHRs and CRMs can save time during implementation and help close potential security gaps. Platforms that support HL7 and FHIR standards ensure data integrity while enabling fine-tuned access control through RESTful APIs [1]. For EHR integrations, SMART on FHIR is the gold standard, requiring strict adherence to OAuth 2.0 flows and PKCE for secure authentication [2].
Connection methods are equally critical. Secure communication channels - such as SSH tunnels, VPNs, or VPC peering - should always be used instead of public internet connections [8]. Additionally, hybrid architecture options can enhance security by separating the control plane (orchestration) from the data plane (processing), ensuring PHI stays within your organization’s secure network [1].
While technical integration is fundamental, the platform's scalability and the vendor's credentials also play a key role in maintaining long-term compliance.
Certifications and Growth Capacity
Beyond technical features, it’s essential to verify that vendors meet documented HIPAA requirements through signed BAAs and SOC 2 Type II certifications [2]. A Business Associate Agreement (BAA) isn’t just a formality - it’s a legal cornerstone of HIPAA compliance. Any vendor handling PHI must sign a BAA before data exchange begins [2]. As Truto emphasizes:
"A signed BAA is necessary, but it is not a substitute for design discipline. A signed contract does not fix broad scopes, raw payload logging, or weak token handling." – Truto [2]
In addition to a BAA, SOC 2 Type II certification provides independent validation of a vendor’s operational security. For example, Truto has successfully completed SOC 2 Type II audits for two consecutive years [2]. Look for platforms that also support data residency requirements and offer automated retention and disposal features to comply with privacy laws and the six-year retention rule [1][3].
Platform Comparison: HIPAA-Compliant Data Integration Tools
Platform Comparison Table
When evaluating HIPAA-compliant platforms, focus on key factors like pricing transparency, the availability of a Business Associate Agreement (BAA), and how well the platform integrates with your existing systems. One critical note: if a platform refuses to sign a BAA, it cannot legally handle Protected Health Information (PHI).
For added security, look for SOC 2 Type II certification, which proves that the platform maintains consistent security controls over time, rather than just passing a one-time audit [10][11]. For even greater assurance, consider platforms with HITRUST CSF certification, often regarded as the "gold standard" in healthcare security [10].
With these criteria in mind, Lead Receipt emerges as a tailored solution for healthcare practices, offering both automation and compliance. Here's a closer look at how it measures up to essential HIPAA compliance metrics:
Lead Receipt: Healthcare Workflow Automation with Built-In Compliance
Lead Receipt is designed to meet strict HIPAA requirements while also addressing the everyday needs of small to medium healthcare practices. It offers 24/7 AI-powered patient engagement, ensuring that your practice stays connected with patients at all times. Unlike many traditional CRMs that charge per user, Lead Receipt simplifies budgeting with flat-rate pricing starting at $300/month for web-based services.
One standout feature is its visual workflow builder, which allows administrators to create custom automations without needing technical expertise. Whether it's setting up automated patient check-ins for recovery programs, sending notifications to family members involved in home care, or prioritizing patient inquiries based on urgency, the platform adapts to your practice's specific needs. Plus, all patient interactions are synced in real-time with your existing CRM and scheduling tools, ensuring data remains consistent and up to date.
Compliance is seamlessly integrated. The Enterprise plan includes advanced compliance features, such as a dedicated AI consultant, unlimited AI calls, and robust integrations. Lead Receipt takes care of encryption, access controls, and audit logging, so you can focus on patient care instead of worrying about security protocols. For practices that need more advanced capabilities, the Professional plan ($750/month) supports up to 100 AI calls daily across voice and chat, offers dedicated phone lines in five languages, and provides priority support.
Administrative tasks currently consume about 45% of healthcare staff time [9]. Lead Receipt alleviates this burden with its AI receptionist, which handles scheduling, patient intake, and inquiries around the clock. This ensures that no patient interaction is missed, even during peak hours or after-hours, helping your team focus on what truly matters - delivering quality care.
Common Mistakes in Healthcare Data Integration and How to Prevent Them
Compliance Features Limited to Premium Tiers
Some platforms market themselves as HIPAA-compliant but place essential security features behind higher-tier plans. This often leads to a frustrating situation: healthcare practices sign up for a basic plan, assuming it meets compliance requirements, only to discover that critical features - like a Business Associate Agreement (BAA), advanced audit logs, or encryption controls - are locked behind premium upgrades. To avoid this, always confirm that the plan you’re considering includes the necessary compliance tools upfront.
Remember, HIPAA penalties for non-compliance are steep. It’s crucial to have a signed BAA in place before uploading any Protected Health Information (PHI). Relying solely on technical security measures without legal compliance won’t protect you [8][13]. These kinds of pricing and integration missteps only add to the risks already highlighted in earlier discussions.
Incomplete EHR and CRM Connections
Integration gaps can also lead to serious vulnerabilities. For instance, some tools may connect to an Electronic Health Record (EHR) system but only sync basic patient information, like demographics, while leaving out critical data such as lab results, medication lists, or care plans. This forces staff to manually input vital details, increasing the risk of errors. Additionally, engineering teams can unknowingly violate compliance rules by logging raw HTTP responses to third-party tools like Datadog or CloudWatch during troubleshooting [2].
To address these issues, consider using pass-through proxies that handle data in memory and immediately discard it, rather than storing PHI in middleware [2]. Implement field-level filtering to remove sensitive information - like Social Security numbers - at the proxy layer before data reaches its destination [2]. When evaluating EHR systems for integration, ensure they’re listed on the Certified Health IT Product List (CHPL). This guarantees they support secure APIs as required by the 21st Century Cures Act [12].
Data Storage Location and Regional Requirements
It’s not just about securely transmitting data - where the data is stored matters just as much. Some healthcare organizations overlook data residency rules, only to later realize their integration platform is storing PHI in international data centers. This could violate state laws or contracts that mandate PHI remain within U.S. borders [13][5].
Many integration platforms use a "store and forward" model, creating secondary "shadow databases" of PHI. These not only increase your compliance workload but also double your exposure to potential breaches [2]. Similarly, relying on uncoordinated methods like fax, email, and portals can create untracked "shadow" data flows that are challenging to secure [4].
To minimize these risks, choose cloud regions that comply with data residency requirements, such as AWS US-East-1, to ensure PHI stays within authorized jurisdictions [13][5]. Opt for Query-in-Place or Zero-Retention proxy models that process data in memory and send it directly to its destination without storing it on disk [3][2]. Since HIPAA mandates a six-year retention period for records, and many platforms only retain logs for one year, set up automated exports to long-term storage solutions like Amazon S3 or Azure Blob [13].
"Simply selecting a 'HIPAA-compliant' platform doesn't automatically make their implementation compliant." - Owais Akbani, Data Consultant, Folio3 [13]
With the average cost of healthcare data breaches reaching $9.77 million in 2024 - the highest of any industry for 14 years running [2] - these common mistakes can lead to severe financial and legal consequences that may jeopardize your practice.
Final Thoughts
Picking the right HIPAA-compliant integration tool means finding a balance between strong security, operational ease, and the ability to grow with your needs. This is especially critical when the average cost of a data breach is a staggering $9.77 million [2].
Your chosen platform should include key features like a signed Business Associate Agreement (BAA), AES-256 encryption for data at rest, TLS 1.3 for secure data transmission, and detailed audit logging. These elements are the backbone of any compliant integration. As Droplet aptly puts it:
"Compliance is a process, not a product. You can't buy HIPAA compliance; you achieve it by building a secure process with the right tools." - Droplet [14]
A secure architecture is also essential. Tools using pass-through or query-in-place models - where data is processed in memory without creating extra copies of protected health information (PHI) - can significantly lower your compliance risks. However, technical safeguards alone aren’t enough. The tool must also be easy to use, as overly complex systems can lead to workarounds that undermine security.
When evaluating platforms, look for user-friendly features like visual, low-code interfaces. These make it easier for your team to quickly adjust workflows while maintaining strict field-level filtering to comply with the "minimum necessary" rule.
For example, Lead Receipt offers healthcare workflow automation with built-in compliance. Their Professional plan ($750/month) includes priority support, call recordings, and lead data handling for up to 100 AI calls daily. For larger-scale needs, the Enterprise tier provides advanced compliance features, unlimited integrations, and a dedicated AI consultant to help your practice grow securely.
FAQs
What exactly counts as PHI in data integrations?
Protected Health Information (PHI) in data integrations refers to any health-related data that can identify an individual. This data is created, shared, or stored by entities covered under HIPAA or their business associates. It includes details about a person’s health condition, medical treatments, or payment information. Examples of PHI are medical records, billing information, and other identifiable health-related data.
How do I verify a vendor is truly HIPAA-compliant (beyond a BAA)?
To confirm a vendor's HIPAA compliance beyond just signing a Business Associate Agreement (BAA), look for specific safeguards. These include encryption of Protected Health Information (PHI) both in transit and at rest, role-based access controls to restrict data access, and immutable audit logs for tracking changes. Ensure they rely on HIPAA-eligible infrastructure and follow the administrative, physical, and technical safeguards outlined in the HIPAA Security Rule. Additionally, practices like continuous monitoring and automated evidence collection can signal their commitment to maintaining compliance over time.
How can we integrate EHR and CRM data without creating “shadow databases”?
When integrating Electronic Health Records (EHR) with Customer Relationship Management (CRM) systems, it's crucial to avoid creating "shadow databases" - unofficial, redundant data copies that can lead to compliance risks and inefficiencies. Here's how you can ensure a smooth and secure integration process:
Use Secure, Direct Pathways: Opt for APIs to enable real-time data sharing between systems. This minimizes the need for duplicate data storage and ensures seamless communication.
Prioritize Data Security: Encrypt all data transfers using protocols like TLS 1.2 or higher. Additionally, enforce strict access controls to ensure only authorized users can access sensitive information.
Leverage Middleware Solutions: Integration platforms specifically designed for healthcare can simplify the process while maintaining centralized and compliant data management.
Conduct Regular Audits: Periodic reviews help identify any issues with data duplication or compliance lapses, allowing you to address them proactively.
Share Only What’s Necessary: Limit data exchanges to essential information only, reducing the risk of unnecessary duplication or misuse.
By following these steps, you can streamline EHR-CRM integration without compromising data integrity or security.